China’s Great Firewall May Be Poisoning the Entire .icu Top-Level Domain Infrastructure Nationwide
DNS interference may have reached the registry nameserver layer, threatening connectivity for millions of .icu domains inside China
Users inside mainland China report that the nameservers for the .icu top-level domain are resolving to the wrong IP addresses — a disruption that, if confirmed at the registry level, could affect millions of registered names
Users in mainland China are reporting that .icu domains are failing to resolve correctly, with network checks suggesting the problem may reach deeper than a typical registrable domain-based censorship block — pointing to interference at the level of the .icu registry’s own authoritative nameservers.
Unlike blocking individual websites, DNS poisoning that reaches the top-level domain (TLD) authoritative nameserver layer can propagate through the TLD’s entire DNS infrastructure, affecting not just targeted users but the caching servers that serve them.
What the records show
According to IANA — the Internet Assigned Numbers Authority, which maintains the global DNS root — the .icu top-level domain is delegated through four nameservers: a.nic.icu, b.nic.icu, c.nic.icu, and d.nic.icu, which should resolve to specific IP addresses operated by CentralNic on behalf of the registry.
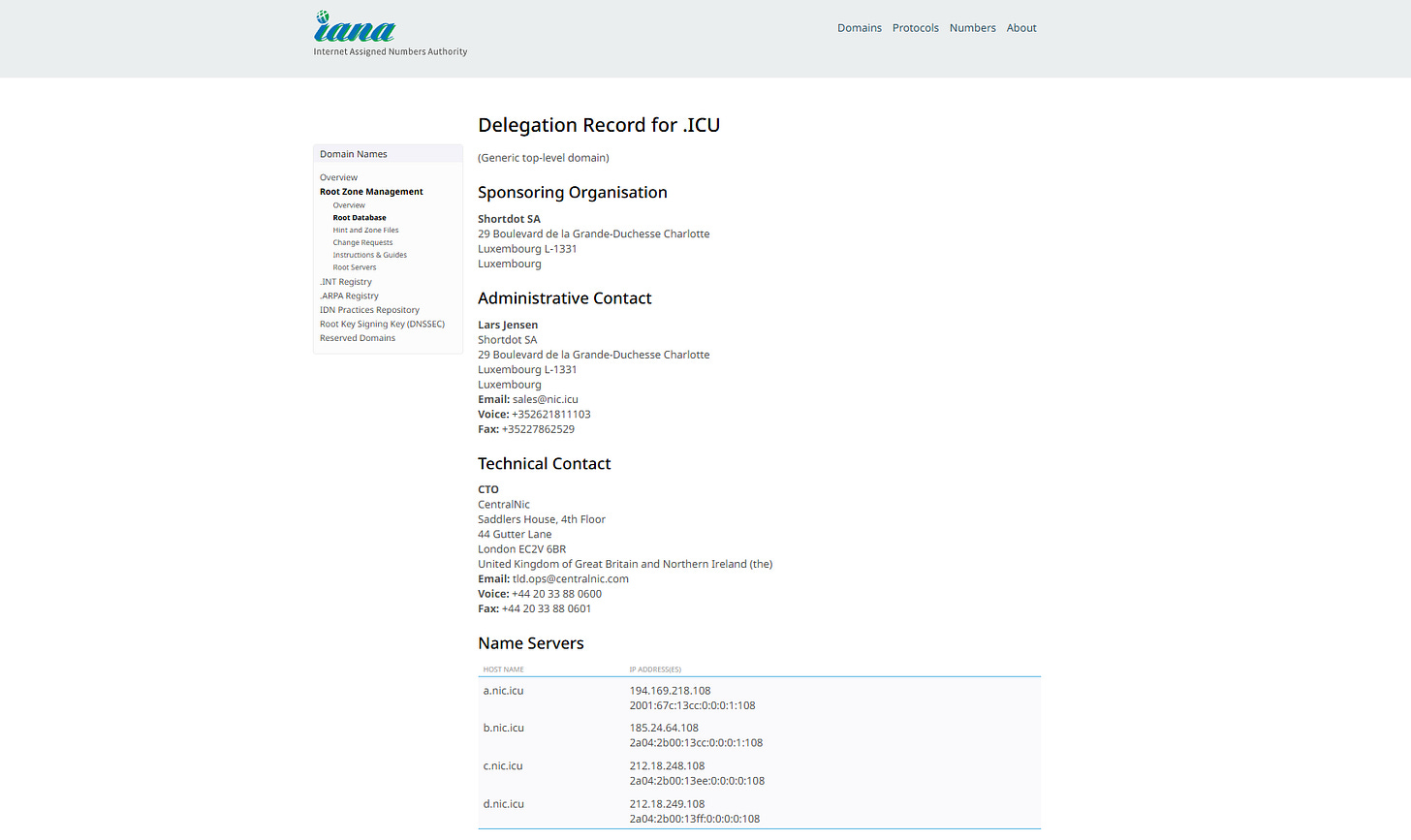
Users testing from Chinese network nodes, using tools like itdog.cn, are instead receiving different IP addresses entirely — including addresses that bear no relation to the registry’s published infrastructure.
At 6:22 a.m. UTC on Tuesday, April 28, 2026, when this publication was written, testing using itdog.cn against one of the authoritative servers, b.nic.icu, by resolving the A record through local ISP DNS servers produced the following result: only 58.13% of attempts resolved to the designated IP address, 185.24.64.108, while the others were polluted.
Among the reported responses, 31.13.94.37 is a known Facebook IP range, consistent with a well-documented pattern in which China’s Great Firewall redirects queries for censored domains to random real IP addresses, a technique that makes anti-poisoning countermeasures significantly harder to deploy than when a fixed set of fake IPs is used.

Shortdot SA, the Luxembourg-based registry operator for .icu, and CentralNic, which handles its technical infrastructure, had not responded to requests for comment.
Why TLD-level nameserver pollution is different
Most DNS censorship in China operates at the level of individual domains — a query for a particular website returns a wrong or blocked IP, while the rest of the internet continues normally. When the Great Firewall observes DNS queries to certain domains, it responds by injecting a poisoned DNS response to the requesting resolver. Due to its position in the network, this typically reaches the requesting resolver before the response from the actual DNS server.
Poisoning the registry’s own nameservers — the a.nic.icu, b.nic.icu, c.nic.icu addresses — is a different order of disruption. Those servers are not individual websites; they are the infrastructure that tells the global DNS system where to find any .icu domain. If those records are being intercepted or misdirected inside China, no .icu query resolved through a Chinese resolver can complete correctly, regardless of whether the individual domain was ever on a blocklist.
Research into the GFW has documented that even when poisoned responses are set aside, the DNS caches of servers inside China can themselves become poisoned — suggesting the attack is not always targeted at individual users, but at the underlying DNS infrastructure.
This is not without precedent. In 2010, a root name server operated inside China began returning poisoned DNS results to global users, preventing users in Chile and the United States from accessing sites including Facebook. The server was shut down to stop the poisoning. In 2014, two-thirds of China’s DNS infrastructure began resolving unrelated domains to a single US-based IP address, causing a widespread internet outage inside China.
The .icu domain and China’s censorship history
The .icu extension is not simply a generic low-cost domain with an outsized presence in China. It carries specific political history.
The 996.ICU project was initiated by an anonymous user on GitHub on 26 March 2019. The person complained that the “996” work schedule — 9am to 9pm, six days a week — recently advocated by some prominent entrepreneurs in the Chinese tech industry risked sending employees straight to the intensive care unit. The name of the domain was the protest itself.
The project spread fast. By 30 April, it had received 240,000 stars on GitHub. Chinese domestic browsers — including Tencent’s QQ browser, Alibaba’s UC browser, and Qihoo’s 360 browser — restricted access to the 996.ICU repository, saying the website contained illegal or malicious information.
In response, workers at Microsoft and GitHub launched a public petition calling on the company to keep the 996.ICU repository uncensored and available to everyone, citing solidarity with Chinese tech workers.
The .icu extension became a template. 611Study.ICU — standing for “study from 6 AM to 11 PM, and end up in ICU” — was launched as a crowdsourced documentation project targeting the enforced schedules of Chinese high school students, with countless students suffering both physically and mentally from the schedule. The project’s revelations that over 2,000 schools had illegally forced students back early for extended study hours triggered public outrage, prompting authorities in at least one Chinese city to issue directives banning early returns.
The .icu extension is also deeply embedded in the Chinese internet commercially. According to domainnamestat.com, the .icu zone has 1,107,698 registered domains to date.
What remains unconfirmed
The reports are circulating on Chinese-language technical forums, with testing tool results as the primary evidence. The claims have not been verified by independent measurement platforms such as OONI or Censored Planet, and no statement has come from Shortdot, CentralNic, or ICANN. It is also possible that what some users are observing reflects localized resolver-level pollution rather than interference at the registry nameserver tier itself — a distinction that matters for the scope of any disruption.
Researchers and domain operators with access to Chinese network nodes can test the behavior directly by querying a.nic.icu from within mainland China and comparing results against the IANA-published delegation record.
Shortdot SA and CentralNic were contacted for comment. This story will be updated as additional information becomes available.